Your home WiFi is broadcasting right now — and someone nearby might be listening.
Most people set up their router once, never touch it again, and assume they’re fine. They’re not. In 2024, cyberattacks on home networks surged by over 30%, and the majority of victims had no idea they’d been compromised until the damage was done. Your router isn’t just the thing that streams Netflix — it’s the front door to every device in your home. Your laptop. smart TV. Even your thermostat.
The good news? Locking it down doesn’t require a computer science degree.
I’ve seen people spend thousands on antivirus software while leaving their router password as “admin123.” That’s like bolting your front door and leaving the back window wide open. Real home network security starts with a handful of deliberate, specific steps — most of which take under ten minutes. In this guide, I’ll walk you through exactly what to do, in what order, so you can stop guessing and start actually protecting your network.
Let’s get into it.
Why Home WiFi Security Matters More Than Ever
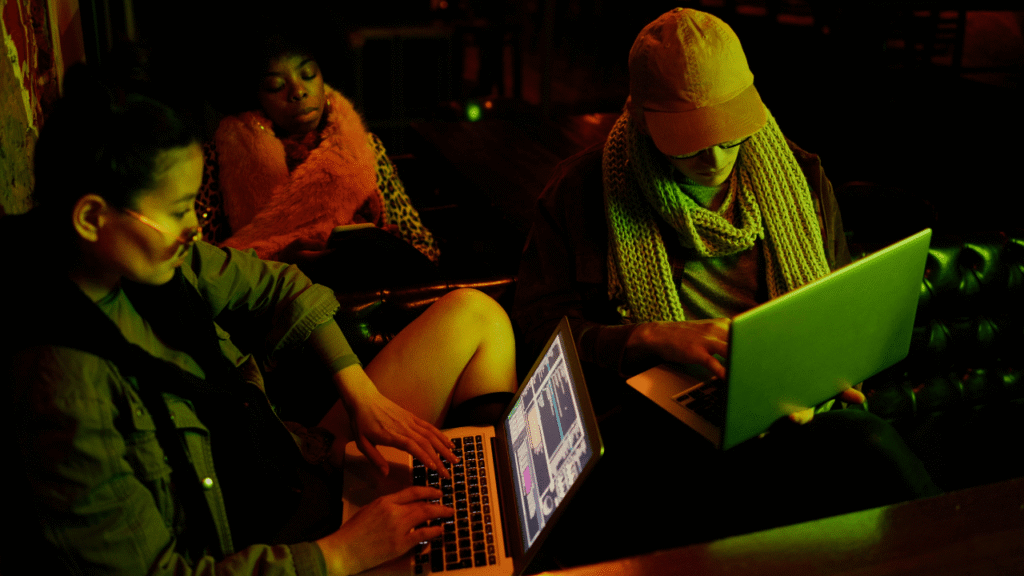
Home networks have never been more vulnerable. The average household now connects over 20 devices to WiFi — smartphones, laptops, smart speakers, security cameras, baby monitors, and more. Every single one of those devices is a potential entry point.
Hackers don’t just target businesses. In fact, home networks are often easier targets precisely because most people assume they’re too small to matter. But attackers aren’t always after your data directly. Sometimes they want your bandwidth for botnet attacks. they want to intercept your banking credentials. Sometimes they just want free internet while parked outside your house.
The threat is real, it’s local, and it’s largely preventable.
What Are the Most Common Ways Hackers Access Home WiFi?
Before you can defend yourself, you need to understand how attacks actually happen. There are four main methods hackers use to break into home networks.
Default Credentials
Every router ships with a default admin username and password — usually something embarrassingly simple like “admin/admin” or “admin/password.” These defaults are publicly documented online. If you’ve never changed yours, you’re essentially handing over the keys.
Weak or Outdated Encryption
Older encryption protocols like WEP and WPA are no longer secure. WEP can be cracked in under a minute with freely available tools. If your router is still running on these protocols, you’re running on a broken lock.
Evil Twin Attacks
This is where a hacker sets up a fake WiFi network with the same name as yours. Devices that have previously connected to your network will sometimes automatically reconnect to the imposter. Once connected, all traffic passes through the attacker’s machine.
Brute Force Attacks
Automated tools can run thousands of password combinations per second. A weak WiFi password — anything under 12 characters or using common words — can be cracked in hours, sometimes minutes.
How to Protect Your WiFi From Hackers: Step-by-Step
Step 1: Change Your Router’s Default Login Credentials
Log into your router’s admin panel. The address is usually 192.168.1.1 or 192.168.0.1 — type it directly into your browser. Once inside, find the admin credentials section and change both the username and password immediately.
Use a strong, unique password. At least 16 characters, mixing uppercase, lowercase, numbers, and symbols. Write it down somewhere physical if you need to. Just don’t leave it as the default.
Step 2: Enable WPA3 Encryption (Or WPA2 at Minimum)
Inside your router settings, look for the Wireless Security section. You’ll see a dropdown for the security protocol. Select WPA3 if your router supports it — it’s the current gold standard. If WPA3 isn’t available, WPA2-AES is acceptable. Avoid WEP, WPA, or TKIP entirely.
This single change dramatically increases the effort required to crack your network.
Step 3: Create a Strong, Unique WiFi Password
Your WiFi password and your router admin password are two different things. Both need to be strong. Your WiFi password is what you share with guests and what all your devices use to connect.
Make it at least 16 characters. Use a passphrase if it’s easier to remember — something like “PurpleCloud!Mountain99Radio” is both memorable and extremely hard to crack. Never use your name, address, or anything a neighbour could guess.
Step 4: Hide Your Network SSID
Your SSID is the name your WiFi network broadcasts to nearby devices. Hiding it removes your network from the list of visible networks that appear on every passing phone and laptop. It won’t stop a determined attacker — but it eliminates casual opportunistic targeting.
In your router settings, look for “SSID Broadcast” and disable it. Your devices will still connect normally since they already know the network name. New devices will require manual entry of the network name, which is a minor inconvenience and a meaningful security gain.
Step 5: Set Up a Separate Guest Network
This is one of the most underused security features on modern routers, and it’s remarkably effective. A guest network runs on a separate SSID with its own password, completely isolated from your main network.
Put all IoT devices — smart TVs, thermostats, cameras, speakers — on the guest network. These devices often have weak security firmware and are common targets. By isolating them, even if one is compromised, the attacker can’t reach your primary devices like laptops and phones. Guests get internet access without touching anything sensitive.
Step 6: Update Your Router Firmware Regularly
Router manufacturers regularly release firmware updates that patch known vulnerabilities. Most people never install them. Log into your admin panel, check for firmware updates, and install whatever is available. If your router supports automatic updates, turn that feature on immediately.
Routers older than five years should be replaced regardless. Manufacturers stop issuing security patches for older models, leaving known vulnerabilities permanently unpatched — no matter how carefully you configure everything else.
Step 7: Disable WPS and Remote Management
WiFi Protected Setup (WPS) was designed to make connecting new devices easier. It was also found to have a fundamental security flaw that makes it exploitable within hours. Disable it. The convenience isn’t worth it.
Remote management lets you access your router settings from outside your home network. Unless you specifically need this feature, disable it. It’s an unnecessary external attack surface that most home users have no practical reason to keep active.
Step 8: Use a VPN on Your Home Network
A Virtual Private Network encrypts all traffic leaving your network, making it significantly harder for anyone intercepting your data to read it. You can install a VPN directly on your router, covering every connected device automatically, rather than installing it on each device individually.
This is especially valuable when working from home or when accessing financial accounts. Even if someone manages to intercept your traffic, encrypted VPN data is effectively unreadable without the decryption key.
How Do I Know If Someone Is Already on My WiFi?
Log into your router admin panel and navigate to the connected devices section. You’ll see a list of every device currently connected to your network. Compare this list against the devices you own. Any unfamiliar device — an unrecognised MAC address or device name — could indicate unauthorized access.
Signs your network may already be compromised include:
- Unexplained slowdowns in your internet speed
- Devices disconnecting and reconnecting randomly
- Unfamiliar devices appearing in your router’s device list
- Router indicator lights active when all your devices are idle
- Unexpected changes to your router’s DNS settings
If you suspect a breach, change your WiFi password immediately and reboot your router. This forces all currently connected devices — including any intruders — to reconnect using the new credentials.
WiFi Security Settings: What to Enable and What to Disable
| Setting | Recommended Action | Reason |
|---|---|---|
| WPA3 Encryption | Enable | Strongest current standard |
| WPS | Disable | Known exploitable vulnerability |
| Remote Management | Disable | Unnecessary external access |
| Guest Network | Enable | Isolates IoT devices |
| Auto Firmware Updates | Enable | Patches vulnerabilities automatically |
| SSID Broadcast | Disable | Reduces visibility to attackers |
| Default Admin Password | Change immediately | Publicly known factory defaults |
| 5GHz Band | Use where possible | Shorter range, less exposure |
Does a VPN Protect Your Home WiFi?
A VPN protects the data transmitted over your network by encrypting it end-to-end. It does not prevent unauthorized users from connecting to your WiFi — that requires strong passwords and proper encryption protocols. Think of a VPN as protecting what travels through your network, while WPA3 and strong passwords protect who can access it in the first place. Both matter. They address different threats.
Frequently Asked Questions
Q1: How do I protect my WiFi from hackers at home?
Change your default router admin credentials, enable WPA3 encryption, set a strong WiFi password of at least 16 characters, disable WPS, and keep your firmware updated. These steps address the most common vulnerabilities in home networks.
Q2: Can someone hack my WiFi without the password?
Yes. Hackers can exploit outdated encryption protocols like WEP, use brute force tools against weak passwords, or leverage router vulnerabilities to gain access without ever knowing your password. Keeping firmware updated and using WPA3 significantly reduces this risk.
Q3: How do I check who is connected to my WiFi?
Log into your router’s admin panel at 192.168.1.1 or 192.168.0.1 and navigate to the connected devices or DHCP client list section. This shows every device currently on your network, including device names and MAC addresses.
Q4: Is hiding your WiFi SSID effective?
Hiding your SSID adds a layer of obscurity but is not a substitute for strong passwords and encryption. It reduces opportunistic attacks by making your network invisible to casual scans, but experienced attackers can still detect hidden networks using packet analysis tools.
Q5: How often should I change my WiFi password?
Change your WiFi password at minimum once per year, or immediately after sharing it with someone who no longer needs access, suspecting a breach, or moving into a new property. Using a password manager makes frequent changes effortless.
Conclusion
Protecting your WiFi from hackers isn’t complicated — but it does require you to actually do it. Most vulnerabilities in home networks aren’t the result of sophisticated attacks. They’re the result of factory defaults that were never changed, passwords that were never updated, and firmware that was never patched.
The steps in this guide take less than an hour combined. In exchange, you get a home network that is genuinely hard to compromise — one that keeps your devices, your data, and your family’s privacy protected.
Don’t wait until something goes wrong. Log into your router settings today, work through this list, and check it off once and for all.
Your network security starts right now — and it starts with you.
→ Bookmark this guide and share it with someone who still hasn’t changed their router password. You probably know at least one person.